Talk 1: Towards an Accountable and Private Internet
Talk 2: Bootstrapping Transparency for Internet Communication
Speaker 2: Dr Chris Pappas, Postdoctoral Researcher, ETH Zurich
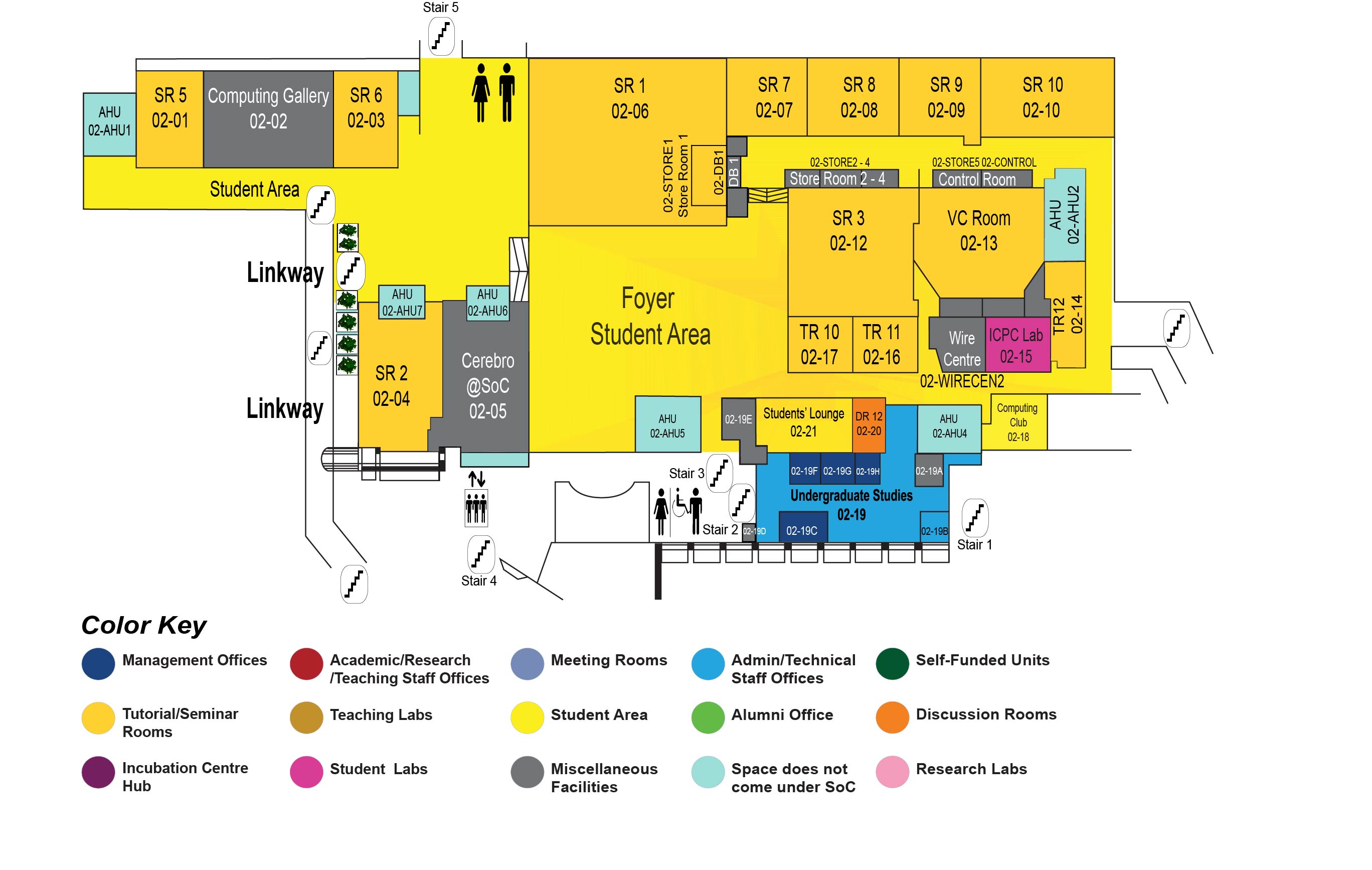
COM1 Level 2
Video Conference Room, COM1-02-13
Talk 1: TOWARDS AN ACCOUNTABLE AND PRIVATE INTERNET
Abstract:
Today's Internet fails to provide either source accountability or privacy; packets cannot be attributed to their source, and communications on the Internet cannot be kept private. Furthermore, even if the Internet can be modified to support the two properties, simultaneously providing both is difficult because they are conflicting. Hence, most future Internet architecture (FIA) proposals have focused on one property at the expense of the other.
In this talk, we explore an FIA that balances between source accountability and privacy. To this end, we propose the Accountable and Private Network Architecture (APNA) that guarantees source accountability while preserving the privacy of the users. Then, we extend APNA to provide stronger privacy guarantees. Specifically, we define a new concept, flow-packet unlink ability - preventing an adversary from linking packets to flows - and extend APNA to achieve flow-packet unlink ability.
Biodata of Dr Taeho Lee:
Taeho Lee is a postdoctoral researcher at ETH Zurich, working in the Network Security Group. His main research area is designing secure future Internet architecture. Specifically, he is interested in designing a network architecture that aims to support both privacy and accountability. Before joining ETH Zurich, he worked as a researcher at Electronics and Telecommunications Research Institute (ETRI) in South Korea. At ETRI, he was part of the future Internet research team that worked on a mobility-oriented network architecture.
Talk 2: BOOTSTRAPPING TRANSPARENCY FOR INTERNET COMMUNICATION
Abstract:
The simplicity of the Internet architecture comes at the cost of transparency for Internet communication:
(i) Receivers cannot explicitly state desired traffic policies for incoming traffic
(ii) Network addresses cannot be trusted enabling attackers to spoof traffic
(iii) The network exposes no information about how traffic is treated and forwarded in the network
In our work, we tackle the problem of enhancing transparency for Internet communication. In the first part of the talk, we describe how transparency can help with flooding attacks. Specifically, we design, analyze, and implement two architectures, FAIR and TRIS, that enable receivers to construct verifiable evidence of misbehaviour at the Autonomous System (AS) level and the host level correspondingly. Next, we take a closer look at replay attacks, which undermine the accountability guarantees of FAIR and TRIS. To this end, we devise and implement a highly-efficient protocol that can drop replayed packets even at today's multi-Gbps forwarding rates.
In the second part of the talk, we argue that increased transparency can help to escape the conundrum of network neutrality. We start by showing that neutrality definitions are problematic and even undesirable. Then, we outline a transparency framework and identify which sub problems have been solved and which remain open.
Biodata of Dr Chris Pappas:
Chris Pappas is a postdoctoral researcher at ETH Zurich, working in the Network Security Group. His PhD thesis work focused on transparency for Internet communication with applications to flooding attacks and network neutrality. Prior to his PhD, he obtained his diploma from the ECE department of the National Technical University of Athens in 2012 and continued working as a researcher until 2013. His research topics of interest include network architecture, privacy, and accountability.

